Mutillidae is a free, open source, vulnerable web-application providing a target for web-security tester. Mutillidae can be installed on Linux and Windows using LAMP, WAMP, and XAMMP.
Username Enumeration :- We have an application that will reveal to us when a username exists on the system which can be used in further step like brute-force account.
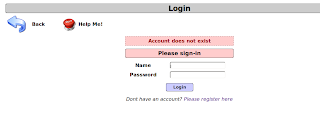
In Mutilliade login page , when you provide valid username & invalid password , web-application reply us that password incorrect.
When we provide invalid username ; then application tell us that Account does not exist.
So by monitoring web-application message one can know that username is valid or not.
First we will examine source code of page ; when we provide valid username reply is "var lAuthenticationAttemptResultFlag = 1" & when we provide invalid username reply is "var lAuthenticationAttemptResultFlag = 0"
var lAuthenticationAttemptResultFlag = 1 It means username exist.
var lAuthenticationAttemptResultFlag = 0 It means username does not exist.
Alternatively we can do this by saving both page (valid username & invaild username) source code in text file & then use diff command.
root@bt:~# diff login password
762c762
< var lAuthenticationAttemptResultFlag = 0;
---
> var lAuthenticationAttemptResultFlag = 1;
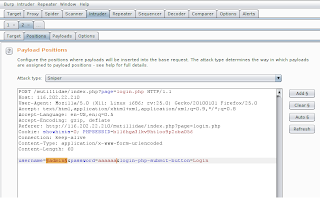
Now Open burpe suite, setup listener ; try to sign in from browser & capture request.
Now right click on request & click on send to inrtuder.
For position we choose only username.
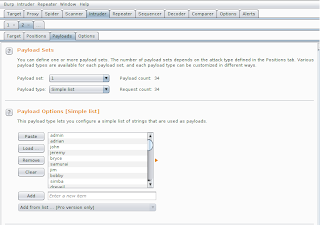
On payload tab ---) payload option ----) load sample username list.
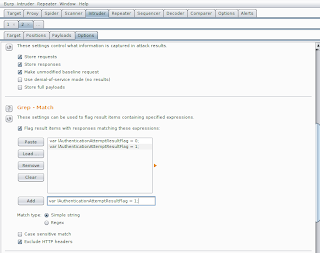
In option tab ---) Grep match ---) Add
var lAuthenticationAttemptResultFlag = 1; var lAuthenticationAttemptResultFlag = 0;
Click on intruder ---) start Attack
Now Burpe make request to login page & examine request & classified responce according to option which we provided.
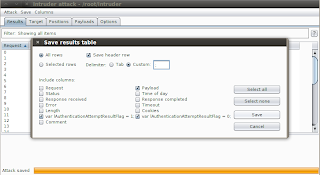
Click on save , result table & Delimiter click on custom & put ";" ,then select column which we need , in this case i select payload,var lAuthenticationAttemptResultFlag = 1,var lAuthenticationAttemptResultFlag = 0 and then save it.
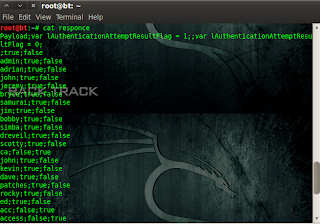
Saved file is look like following format.
In file first is username ; then true means username exist , false menas username is invalid. So now we only need entry which second column is true.
So i saved this value in another temp file from where you can extract username from file using delimiter. I used simple python script for this purpose.
Finally we got list of username which exist on system.
Username Enumeration :- We have an application that will reveal to us when a username exists on the system which can be used in further step like brute-force account.
In Mutilliade login page , when you provide valid username & invalid password , web-application reply us that password incorrect.
When we provide invalid username ; then application tell us that Account does not exist.
So by monitoring web-application message one can know that username is valid or not.
First we will examine source code of page ; when we provide valid username reply is "var lAuthenticationAttemptResultFlag = 1" & when we provide invalid username reply is "var lAuthenticationAttemptResultFlag = 0"
var lAuthenticationAttemptResultFlag = 1 It means username exist.
var lAuthenticationAttemptResultFlag = 0 It means username does not exist.
Alternatively we can do this by saving both page (valid username & invaild username) source code in text file & then use diff command.
root@bt:~# diff login password
762c762
< var lAuthenticationAttemptResultFlag = 0;
---
> var lAuthenticationAttemptResultFlag = 1;
Now Open burpe suite, setup listener ; try to sign in from browser & capture request.
Now right click on request & click on send to inrtuder.
For position we choose only username.
On payload tab ---) payload option ----) load sample username list.
In option tab ---) Grep match ---) Add
var lAuthenticationAttemptResultFlag = 1; var lAuthenticationAttemptResultFlag = 0;
Click on intruder ---) start Attack
Now Burpe make request to login page & examine request & classified responce according to option which we provided.
Click on save , result table & Delimiter click on custom & put ";" ,then select column which we need , in this case i select payload,var lAuthenticationAttemptResultFlag = 1,var lAuthenticationAttemptResultFlag = 0 and then save it.
Saved file is look like following format.
In file first is username ; then true means username exist , false menas username is invalid. So now we only need entry which second column is true.
So i saved this value in another temp file from where you can extract username from file using delimiter. I used simple python script for this purpose.
Finally we got list of username which exist on system.