Today is the age of computer and internet. More and more people are creating their own websites to market their products and earn more profit from it. Having your own website will definitely help you in getting more customer purchasing your products but at the same time you can also also attract hackers to play around with your site. If you have not taken enough care to protect your site from hackers then your business can even come to an end because of these hackers.
Before you hack into a system, you must decide what your goals are. Are you hacking to put the system down, gaining sensitive data, breaking into the system and taking the 'root' access, screwing up the system by formatting everything in it, discovering vulnerabilities & see how you can exploit them, etc ... ? The point is that you have to decide what the goal is first.
The most common goals are:
1. Breaking into the system & taking the admin privileges.
2. Gaining sensitive data, such as credit cards, identification theft, etc. - not recommended
You should have all of your tools ready before you start the next steps too hacking. There is a Linux version called Backtrack. It is an operating system that comes with various security tools that will help you break into systems.
You must decide how you are going to achieve your task. Plan. There is a common methodology followed by hackers, I will mention it below. However, you can create your own methodology if you know what you are doing.
Common steps to be taken for hacking a system:
1. Reconnaissance (footprinting)
2. Scanning
3. Ports & Services Enumeration
4. Vulnerability Assessment
5. Vulnerability Exploitation
6. Penetration and Access
7. Privilege Escalation & owning the box
8. Erase tracks
9. Maintaining access
The above methodology can change based on your goals.
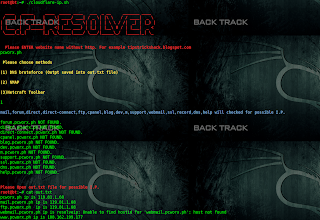
Before you break into a system, you have to collect as much info as you can on the system and target. You have to study your target well before you hack. This step is called reconnaissance. Reconnaissance is achieved by using techniques & tools that are undetectable by the target. You are gathering your target's info that is publicly published, e.g. browse your target's website and finding they are looking for an SQL employee and Windows server admin, then you get a hint that they are running Windows Server & do SQL's. This is called a "passive" action.
Lets see an example of active action. Example of active action: Call the company to obtain some info, visit the company, email employees to get some info, go to the target's website and read its source code. In other words, passive action means you gather info in a non-intrusive manner. Active action is a step further, such as talking to the company as if you are a customer, things like that. It is not really important to know what action is passive and what is active, the main goal here is to gather info. Simple huh? Good, let me go deeper little bit.
In passive reconnaissance, there is a 0% chance of getting caught, as you only target publicly available info to give you the feel on what your target looks like. The type of info you can gather through passive recon. are, names, phones numbers, location addresses, partner networks, and much more. This can aid you when you want to do some social engineering! Hence, sometimes you can get some non-public info that's revealed when you do passive reconnaissance. There are several tools that help you with passive reconnaissance, such as WhoIs (who is). WhoIs helps you obtain extensive info, such as names, domains of the target, etc. Other great tools are, Sam Spade, domain tools, and Google(can reveal lots of target subdomians & many more).
Active reconnaissance goes beyond the passive nature, such as communicating with the target without being caught, such as scanning. Anything not discovered in IDS(Intrusion Detection System) is considered active. You have to think of ways to extract info of the company in a normal way, public by going a little bit deeper than passive recon. E.G. You can go to the physical location, do some social engineering, email staff, communicate with employees based on the info you've gotten on your passive recons. Things like that!
Example of some techniques for active reconnaissance, such as banner grabbing, view company's public website source code and directory structure, social engineering, shoulder surfing, etc.
What the heck is banner grabbing?
You let the server send you a block of information that tells you OS version of your target system & various association with it
Banner tells OS version and various association. Anything listening on a "port" can determine the operating system (OS) "the port" is running on, this called fingerprinting. In other words, fingerprinting is the process of determining the operating system (OS) or applications used by a remote target.
Learn more about banner grabbing:
http://www.net-square.com/httprint/httprint_paper.html
What is shoulder surfing?
Simply, stand behind a person's shoulder and see what the guy is doing & typing on the keyboard. This can happen in a wireless network area where everyone is using a laptop in public areas.
In summary, reconnaissance is one of the most important steps in hacking. The main concept is to gather all the info that is publicly available or easily obtainable. Info that we gather will help us in social engineering and research purposes which will lead you to very critical info about the system. It starts by obtaining names, phones, emails, IP range, domain structure, and so on.
let me show you how banner grabbing is done, telnet into your target server on port 80 as the following, go to command line or terminal and type
telnet xx.xxx.xxx.xxx 80
Now the connection is established, that stupid server thinks you are a web browser connected to it, it waits for you to enter commands so the server can you give you info about your request. In this situation, you have to write a command that says "Hey you web server, give me the content of such and such website". However, we do not really want to visit the website through telnet, do you? You can just go to the web browser and request the website from there. Our purpose here is to freak the server out enough, so it spits back a code that says, hey! this doesn't work but here is some info that might help you do some troubleshooting. This technique allows you to fingerprint various components of the target system.
Note: instead of telnet xxx.xx.xxx.xx 80, you can do nc xxx.xx.xxx.xxx 80! It's the same thing ... nc stands for netcat ... xx.xxx.xx.xxx represents the IP address of the target system.
After you do telnet xxx.xx.xxx.xxx 80, the remote sever will wait for you to enter a command. Type this:
HEAD / HTTP/1.0
Then you will get a reply looks similar to:-
HTTP/1.1 200 OK
Date: Mon, 16 Jun 2003 02:53:29 GMT
Server: Apache/1.3.3 (Unix) (Red Hat/Linux)
Last-Modified: Wed, 07 Oct 1998 11:18:14 GMT
ETag: "1813-49b-361b4df6"
Accept-Ranges: bytes
Content-Length: 1179
Connection: close
Content-Type: text/html
So the header response brought back some important info that says, the server runs: Apache/1.3.23 in UNIX OS for Red Hat distribution of Linux.
OR you might get header that looks similar to the following:
HTTP/1.1 200 OK
Server: Microsoft-IIS/5.0
Expires: Tue, 17 Jun 2003 01:41:33 GMT
Date: Mon, 16 Jun 2003 01:41:33 GMT
Content-Type: text/html
Accept-Ranges: bytes
Last-Modified: Wed, 28 May 2003 15:32:21 GMT
ETag: "b0aac0542e25c31:89d"
Content-Length: 7369
It means, the server runs: Microsoft-IIS/5.0 in Win 2000 or Win 2003 (we don't the Windows version yet).
OR you might get header that looks similar to the following:
Date: Thu, 04 Dec 2008 02:18:46 GMT
Server: Apache/1.3.41 (Unix) PHP/4.4.8 mod_gzip/1.3.26.1a mod_log_bytes/1.2 mod_bwlimited/1.4 mod_ssl/2.8.31 OpenSSL/0.9.8b
Last-Modified: Thu, 10 Jul 2008 23:34:28 GMT
ETag: "c9865b-d91-48769c84"
Accept-Ranges: bytes
Content-Length: 3473
Connection: close
Content-Type: text/html
It means, the server runs: Apache/1.3.41 in UNIX box, running PHP/4.4.8
Ok, you get it now?
lets say our target got the following version: the server runs: Apache/1.3.41 in UNIX box, running PHP/4.4.8
At this point if you know any vulnerabilities for this particular OS or this particular Apache or PHP. You can start the exploitation process...
Another example, use program called Sam-Ppade which gives you alot of info about your target. The target does not know actually what we are doing against their server, since they haven't seen anything been triggered by IDS or Firewall.
*What is the difference between IDS & Firewall?
An IDS (Intrusion Detection System) may only detect and warn you of a violation of your privacy. Although most block major attacks, some probes or other attacks may just be noted and allowed through. There's also an evolution of the IDS called an IPS (Intrusion Prevention System) that watches for the same things an IDS does, but instead of just alerting, it blocks the traffic.
A good firewall will block almost all attacks unless specified otherwise or designed otherwise. The only problem is, the firewall might not warn you of the attacks and may just block them.
It may be a good idea to have both an IDS and a Firewall, because the IDS will warn you and then the firewall will block the attack. Over the years, firewalls have gotten more complex and added more features. One of these features is actually IDS - today you can have a firewall that already has IDS(Firewall/IDS's are combined into one internet security program).
Learn more about banner grabbing:
http://www.net-square.com/httprint/httprint_paper.html
To learn how to do it through Google, you need the following book:
http://www.amazon.com/exec/obidos/ASIN/1.../ref=nosim
Note: the book in amazon is just an example for you to give you an idea of what kind of book you should be looking for - if you are interested.
Alright, now you at least have an idea of what reconnaissance is! lets talk about scanning...
When you scan your target's network, you actually start touching the system. Scanning a network determines what's in there, scanning network gives you the feel of how your target's network is laid out, if there are multiple subnets, which hosts are alive, check ports, see if system is alive, discover available hosts & get info about the discovered hosts. There are thousands of tools can be used to scan networks! Scanning a network can easily get picked up by IDS. Anyhow, no one will pay attention except if you do it over and over because scans happens on such a regular basis on the internet. Therefore, people who read the logs, I mean the webmaster won't really pay attention to every single scan that occurs, so you don't have to worry. There are ways to avoid being picked up by IDS. After you finish scanning, you will gain a list of network nodes that exists there.
"Node" is an active electronic device that is attached to a network, and is capable of sending, receiving, or forwarding information over a communications channel. If you want to learn more, Google it or visit http://en.wikipedia.org/wiki/Node_(networking) ...
Ok now we want to discover live hosts via scanning. This is the first action taken against your target's network. Depending on what method of scanning you use, you can be detected by IDS. Most admins will ignore detections because it happens alot unless something abnormal happens.
There are various scanner tools, e.g. Nmap, Superscan, and many more. There are various scan methods, some are stealthy, others are not.
Before I talk about various scanning methods, let me explain to you about TCP connections basics. When you scan your target using TCP communication, there are six TCP flags that can be utilized during packet transmission (packets get transmitted during scanning process). A flag will indicate whether the sent packets are syn, ack, fin, urg, psh, or rst packets. These packets sets you in a position on how you want to communicate with the remote host. You can get different info depending on the flag you choose for the scanning.
TCP establishes three handshakes, syn, syn-ack, ack. What are they?
When you scan your target using TCP communication, you send a syn packet(syn request), and then target sends you back an ack packet with a syn packet. Now, you send an ack packet to the target. So now both machines establish the connection well, like they have made a well established tunnel for a proper guaranteed communication without losing any packets during communicating with each other. A hacker can get caught easily if he uses this method to hack other systems illegally.
Hackers use non-standard combination of these six flags, which gives them info that are not normally available to the public.
Have you heard about syn flood?
Syn flood is done by utilizing three handshake by sending "syn" request to the target, so the target receives a syn request and send an a syn-ack back to the originator(you). You ignore the target syn-ack request - when you ignore it, then the three handshakes is not completed, this is called a half open TCP connection - In theory, when the target sends you syn-ack, the target allocates some RAM on its machine.
The amount of RAM on the target machine must be open until it gets response (ack packet) back from you because till now only two handshake has been made,so the TCP connection process is not completed yet. However, there is always a time limit for the RAM to be opened, so if 30 secs passed by & the target did not get the ack from you, the connection will abort (failed TCP handshake - timeout) & RAM will be allocated.
The idea here is to send hell a lot of packets in few secs so in 30 secs, you can send 40 million packets(lets say one packet size is 1kb) which is heavy on the RAM since the RAM might not have enough memory to carry 40 million packets. Therefore, you force the target to make half open TCP connection attempts, so definitely the target machine will stop responding to legitimate request. In other words, if you send 40 million syn requests to that remote host, it's going to allocate a hell of a lot of ram for those requests. After a while, it's going to eat up all of the ram. Thus, target system goes down. This is called syn flood attack.
In short, syn flood attack makes the system (i.e. the IP stack or kernel) chokes on the memory allocations (or simply runs out of memory) or the target application (i.e. web server) chokes on the processing load. You got it? Or not yet?! Syn flood is an old technique i just mentioned it here for illustration purposes.
General Information: These days, SYN floods are used to make systems inaccessible. They have a limited number of half open connections, you use them all, and they can't accept any more SYNs. But again, modern software throws away old SYNs once the limit is reached. Note that different systems will behave differently.
If you interested in learning more about syn flood, visit
http://tools.ietf.org/html/rfc4987
Lets talk about the most common TCP Scan types. There are full scan, half open scan, stealth scan, Xmas scan, and ack scan.
Full scan: this completes 3 way TCP. it is the most effective & gives more accurate results. However, it is not safe and easily traced and detected.
Half open scan: it is the second most effective scanning method, only uses first part of the handshake to get syn-ack but does not send 3rd part (ack) back to the remote host. The idea here is if the remote replies back to you after you have sent syn request, this means the port - we sent the syn to - must be open.
Stealth scan: the idea here is to scan ports randomly(not in sequential order) & reduce the speed of scanning. If you scan all port from 1 to 65536 in sequence, your more visible to be detected, and usually scanning happens so fast, which is unusual since regular program does not connect to port that fast, so this can make it easier to be detected. Therefore you have to scan ports randomly & reduce the speed of scanning. To avoid IDS, you should not use full connection scan with stealth scan, you can use half-open scan(syn). syn is considered a stealth scan. In fact, syn scan is called syn-stealth scan, or you can use Xmas scan with stealth scan which helps you to evade detection, things like that! you get my point i guess.
Xmas scan: uses fin, urg, and push flags which are used to bypass some firewalls. Xmas scan works with UNIX system, it does not work with Windows system.
Ack scan: this helps you evading IDS not to get you detected. You send only an ack packet to your target, your target won't know how to deal with it since there was no handshake. Thus, ack scan causes open ports in your target machine to return a reset packet(rst), rst packet gives you a hint that the port or service is not filtered between point A and point B, which usually firewall resides in between! Since the port replied you with rst packet this means there is no firewall between A(your machine) & B(port or service on the target machine) and rst packet also gives you an insight that the target port is open ;-). If there is a firewall, your ack packet would not reach to the target port & because of that you won't get any rst packet. In addition, rst packet helps you identify what system is running on the remote host.
These are the most common method of scans, there are hundreds of scanning methods! Nmap allows you to set your own custom scan type e.g. instead of sending ack flags only, you can send ack flag and rst flag together and see what you get back from target ...
OK! we have talked about how TCP scanning works in general. Now, I will be talking about UDP & ICMP Scanning ... UDP and ICMP connections most of the times are blocked at the firewall level & even at the host level in some cases. We are going to scan on hosts & ports that respond via UDP. When you scan your target via UDP, there are many problem will occur during that process e.g. you can scan over the ports via UDP, assume you scanned port 1, and port 1 is closed, then host will send ICMP unreachable back to you, which gives an insight that port is closed because you didn't get any UDP response back from target! Making sense,right? Unfortunately, we will never get a response back from target to ensure you that port is open!
That's how UDP call works, send the packet & forget it. Lets say we come across port 21, and 21 is open, then port 21 on target machine will not reply back to you because UDP does not give you the guarantee the delivery packets during communication process, it just send the packet and forget, unlike TCP which guarantees the delivery of packets with no loss or corruption. Since we didn't get reply back, then we can assume the port 21 is open *OR* maybe port 21 is closed and ICMP reply got lost somewhere so we didn't get it! A general rule, when you don't get a reply you assume port is open.
Some high professional security person purposely configure ports to not respond to UDP scanning. ICMP scanning is as same as UDP. ICMP scanning is noisy & can be picked by IDS very easily because ICMP sends random several pings to the network instead of a single host (ICMP scanning does a 'ping scanning' - sends ICMP packets - to the whole network instead of a single host). After you finish ICMP scanning, based on the replies you get back from the live hosts, then you can determine that your target network is listening for ICMP traffic and you might to do some exploit based on that. Unfortunately, there aren't alot of ICMP exploits going around, so you are just going to use ICMP for network enumeration, you just do it to see what hosts are up, host A is up , host B is up and host C is up, they are replying for my ICMP. Thus, this let us know these 3 hosts are running on the targeted network and potentially can be a target for us. IDS's are always listening for network scans & alot of network scanners provide a support for ICMP scanning, but do not have a way to make it stealthy! Therefore, ICMP can turn on the IDS alert which tells the security person there is somebody scans your whole network.
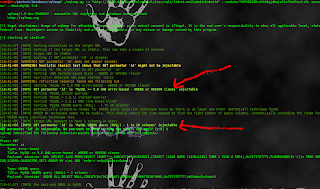
Nmap is a great tool that is very popular, it is usually used to scan networks, hosts, ports, and does alot of other stuff. It is very intrusive tool and considered a hacking tool. Using Nmap against systems you don't own or don't have permission to scan can be considered illegal. Lets see examples of some scanning method!
Example of ICMP Scanning(-sP) - this is called ping scan
nmap -v -sP xx.xxx.xxx.xx > filename
Nmap: represents the program we are running which Nmap.
-v: for increased verbosity, which means bring me extra details of the targeted system. (Optional - as far as i know)
-sP: the flag that determines the scanning method.
x's: target IP address.
> filename: output the results to the newly specified file name. In other words, save results in a file (Optional)
This above command shows you the systems that are up and running, so this shows what is available to us on the targeted network. As a result, you will get simple info that shows you there number of IP addresses that responded to ping request - Note: there could be alot more machines out there that are not responding to ICMP scanning.
Lets see an example of UDP scan, UDP scan not so speed.
nmap -v -sU xx.xxx.xxx.xx
Results of UDP scan(-sU) give more info than ping scan(-sP). Keep in mind there could be hundreds of other ports are listening on the system which simply don't respond to UDP connection.
Useful sources relates to scanning methods via Nmap:
http://www.nmap-tutorial.com/pdf/nmap-tutorial.pdf
http://www.petri.co.il/port-scanning-with-nmap.htm
ALRIGHT, now you have a good basic understanding about scanning! Next, i will be talking about fingerprinting!
Now lets get deeper! By now we have determined what nodes are running up on the network. So we are ready to gather large info on those live systems we discovered in the previous steps. Ok! now you need to discover what services (application) are running on your target's host. Every (or at least many) port has a service running on it. For example, web server usually are running on port 80. What we have to do is scan ports, see what kind of services(applications) are running on them, try to grab the versions of the services, this will help you to determine the OS as well. This is called 'Port & Service Enumeration(fingerprinting)'. We have to do this step to understand what potential vulnerabilities your target has & how to exploit them.
Assume after we have scanned our target system, we found our target runs "IIS 5.0 Server" on "port 80". Based on the scanning result, you can say the target server is running IIS 5.0(IIS is set of Internet-based services, IIS is the second most popular web server - IIS is a Microsoft product), it is known IIS 5.0. has too many vulnerabilities & IIS 5.0 runs on Windows 2000, which Windows 2000 by itself has hundreds of vulnerabilities..
In other words, lets scan ports and services, and do OS fingerprinting, lets identify services on those live host in our target network. Once we know what services are running and what OS are running then we can start exploiting these services! - 'ping/port/service' scans are frequently run together using the same tool.
NOTE: Identifying ports & services is the most critical part in hacking... PERIOD
OS fingerprinting is used for determining OS type and version, then we exploit vulnerabilities that resides into the OS. When you fingerprint a target, your targets' OS can be known from the TCP/IP stack, so fingerprinting happens on TCP/IP stack. Why? Because each OS has a unique implementation of TCP/IP, so TCP/IP stack is implemented differently from OS to OS, so an exact same query sent to one machine the respond of the result will be different than the other machine. Therefore, based on the response this can help the scanner determines the OS of the target, because every OS has its own unique response when you do OS fingerprinting request.
When you do a default install of OS, certain services will be installed by default, services that are needed for that OS to work properly, e.g. ports
137,138,139,and 445 which all combined together to produce Win 2000 OS or above. Another example, a combination of 139 and 445 can determine a certain version of windows such as Win XP or Win 2003, there are lots of ways to determine OS. Another example, if you see a service MS SQL is running on a certain port, you can determine the target OS is not in *nix family, it is in a Win family cause the target is running a Microsoft sql product. Thus, we can say port enumeration or service enumeration can help you in determining OS.
There tons of popular scanners out there:
SuperScan - Works good on Win OS.
Nmap - Works on *nix & Windows, *nix version is much more stable than Win version.
Most scanners offer full, half, stealth, and UDP scans.
You are goning to spend most of your time scanning your target machine to know whats available there, so you can exploit the vulns & penetrate the system. Therefore, you have to do some exploration on scanning methods & decide which method of scanning you feel more comfortable with...
Lets see an example of enumeration style scanning. Just keep in mind, this can be considered hacking! Make sure you do to your system, not somebody's else.
This is kind of a stealth scan:
nmap -v -sS -A -sV xx.xxx.xx.xx > filename
This above request gives you very specific details about your target. sV is for version information identification. Check out the manual to know what these flags do - type "man nmap" to see the manual...
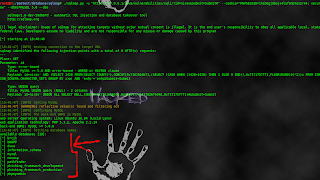
Alright, after we have fingerprinted services & OS, now its the time to check for various vulnerabilities against application(services) & OS running on the target system. This is called vulnerability assessment. To do vulnerability assessment, you can use the tools available, such as Nessus. Nessus is free vulnerability assessment, huge database, its the best assessment tool.
Lets scan vulnerabilities on the target system. Lets say target system is Win 2000 SP1 IIS 5.0, Nessus goes back to its database and check the vulnerabilities for Win2000 & IIS 5.0. If there are no vulnerabilities discovered,the vulnerability assessment tool actually can't catch it. However, if Nessus couldn't find matching vulnerabilities for the target system, it will let you know if the system has some security issues or not. Such tools are considered as Automated Vulnerability Assessment Tools. You have to know about the target system OS so you can do vulnerability assessment on it. There are vulnerability assessment OS specific, e.g. MBSA tool (only scans Win OS).
NOTE: you can do vulnerability assessment manually, this depends on you and your skills. By doing it manually, you can discover vulnerabilities that nobody knows about, and you can use it for your own use. It is a powerful and very discrete.
After we determined what systems & what services contain what vulnerability, then we can exploit it (means take a chance of this vulnerability to achieve what you want).
common vulnerabilities out there are:
OS vulnerabilities
Webserver vulnerabilities
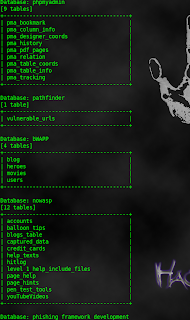
Database vulnerabilities
TCP stack vulnerabilities
Application vulnerabilities
Malwares, viruses, trojans, can be used to exploit vulnerabilities.
There are several automated vulnerability scanners, such as Nessus, Nikto. Security websites is a good resource for vulnerabilities as well, e.g. bugtraq, CVE(Common Vulnerabilities and Exposures) sites, etc. Another good source to find vulnerabilities is hacker web sites.
Lets talk about the tools:
*Nessus - this is a great vulnerability assessment tool. However, in a lot of cases it will perform exploits to see if the OS or service is actually vulnerable or not.
*Metasploit Framework - this is not vulnerability assessment tool. It is an exploitation tool, it contains hundreds of exploits helps you to exploit the system by using a nice selection of tools.
I will explain shortly about the common vulnerabilities...
OS Vulnerabilities: OS exploits are used to gain access to the system. OS exploits can used for DoS attacks too. watch the video tutorial. Most OS holes exist from default configuration, services and applications.
Webserver Vulnerabilities: webservers are the most targeted section. All people contact the webserver, thus you never know the diffference between a hacker and a normal user. Webservers examples, Apache, IIS, and Tomcat. After you exploit the vulnerability in your target webserver, you can gain many different things, such as root access(the gist), website defacement, DoS(put the server down), theft or alteration data on server, or further penetration into the network.
Webserver is a great place to start when you want to do a penetration test!
Database Vulnerabilities: those software vendors who create databases applications such as SQL, Oracle, etc - they dont have security in mind, they care more into efficiency and how to make it easy for the users to handle with the database. They care about making their customers happy without giving that much attention in security issues!
TCP Stack Vulnerabilities: this is not a common used method to hack systems. Google it!
Application Vulnerabilities: some examples of application vulnerability, buffer overflow, weak authentication mechanisms, poor data validation(the most common one), and poor error checking.
ALRIGHT, to discover these vulnerabilities on the target machine you need to do vulnerability assessment. This can be done in two ways, manually or automatically. Manually means you try to discover a vulnerability. by yourself which eventually you will have a vulnerability that nobody else knows about and you can use it for yourself or publish it to security sites. Automatically means you rely on a tool that searches for vulnerabilities in the target machine, this tool has a database full of vulnerabilities, so this 'tool' will only inform you the vulnerabilities found in the target machine by relying on 'its' database. We are going to talk about auto vulnerability assessment. The most common and wonderful tool is Nessus, its free open source code!
A lot of common sense comes into play when analyzing vulnerabilities, for example you do not look for a database vulnerability in a webserver, things like that. Another resources, OVAL - gives you a good and basic foundation of vulnerabilities assess. methodology, FrSIRT - keeps track of vulnerabilities and make exploits of these vulnerabilities, you can join a paid subscription and then browse vulnerabilities available in their database and download exploits this is a good source for hacking or security, and websites for posting exploits such as milw0rm, hacking sites.
Lets have a closer look at nessus tool, nessus is client/server architecture. The process of setting it up is cumbersome. Nessus have about 9000 plugins, therefore it takes time to perform the assessment. Results can be reviewed in a report. The report includes the vulnerabilities found on the target machine with a short description about the vulnerability.
Note: you can enable several plug-ins in plugin tab. You can specify range of ports through scan options. To specify the target, you should go to the target tab.
Once we have done the vulnerability assessment, and knew what vulnerabilities exit. We start gathering exploits of the found vulnerabilities to penetrate the system.
Lets talk about penetration and access! After all information we have gathered previously, its the time to break the system with the exploits you have.
Its the time to stop gathering information and start breaking into system. The ultimate goal is to gain the highest level of permissions. Try to use undiscovered techniques and methods. Think out of the box!
Some of exploits that enable penetration are:
*Buffer overflows
*Stack exploits
*Web vulnerabilities
*Services/apps that allow unauthenticated access.
Aside from the standard methods of penetration, lets see an penetration methods, here are some examples:
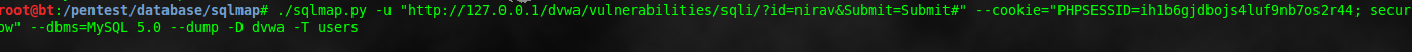
*SQL Injection - ability to change queries in the application before its sent into database.
*Application Error Handling - this can result DoS. Probably one of the most common vulnerability you can find in corporate arenas.
*Directory Traversal - browse directories you should not be able to do so on.
*Malformed Packets - one of the more difficult methods of penetration, requires very extensive knowledge of how TCP packets are assembled and disassembled. But once you get used to it, its probably the most effective ways of hacking.
*Bypassing Access Controls - password cracking is most common means of accessing systems.
*Social Engineering - i guess you know what it means.
*Sniffers - take passwords right off the wire, a lot of protocols and applications such as http & ftp communicate passwords over the wire in plain text.
*Session hijacking - it is similar to sniffers, but you don't gain a password because we take off the entire session, hijack the slave's session & act as you are him.
Usually when you get passwords, you get it encrypted, or hashed or hidden in some way or another. Password cracking can be done in several ways, examples:
*Brute Force Attack - Every password, can and will be broken by brute force attack. It is about the time. Depends on the size of the password.
*Dictionary Attack - less effective than brute force, relies on list of words or phrases.
*Hybrid Attack - combination of different tools. It is a combination of effectiveness of brute force and dictionary attacks & often using other attack mechanisms, such as cryptanalysis attack (one of the hybrid attack).
You should know that when you do sniffing, you often get usernames & passwords in plain text. However, you can get encrypted passwords from sniffing as well. You will need to use of the cracking techniques discussed above. Sometimes cracking an encrypted passwords can take secs, hours, days, months, or even more!!!
There is a great software called "Cain & Abel", it sniffs passwords from the wire, cracks it, etc. Once you install it, go to sniffers tab, then move to the found passwords in cracker tab to see what you have got! There is a lot to it. You should know these techniques as a security person cause if you don't know it, a black hat will take care of it.
Now, assume we already have hacked the system. We will try to do different things, such as getting the root, etc. Penetration & compromise have differences in the meaning. Hacking into system does not mean you have compromised (taking the full control - take over) the system. After you penetrate the system, you can grab the session between client and server, e.g. you keep listening on login sessions, so when the remote user login to Google, the session is dropped to you, once you get the session, the remote user won't be able to get into his account he/she will see at page goes blank (disconnected), so he/she may think its a problem in a connection, thus he/she tries to login again & everything works fine! BUT you already got his session, you won't have to go through login page when you want to see his/her email inbox, cause its already among the whole session you have taken.
Another way to do this, lets say the attacker has compromised the user's system, thus the attacker can let the session drop on his machine, then he takes the session, reads and saves it. After that, he redirects the user to the server, this step will make everything works ok like nothing wrong happen.
Lets see an example of the above explained steps, after attacker installs "Cain & Abel" application, he moves to "attack base system" & click the sniffer button at the top & click the yellow button(APR Poisoning Button) besides the sniffer button. This APR Poising button trick the attacked system to talk to the attacker instead of normally who it talks to. For testing purposes, go and add various system addresses(IP's) to the list. Let say one of the user amongst those targeted IP's logon into 'Google', at the authentication process you will notice varies pieces of info comes to you. You are gathering info by getting into the middle of the communication process. Now view the files you have got in the list, you can see among the lines the username & password of the users' 'Google' account in plain text! So how dangerous this can be to your privacy! So be careful....
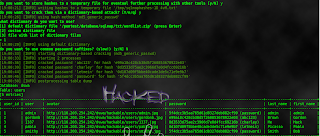
Once the hacker gains access to the system. He aims for admin(root) access. He moves up from guest level, to user level, up to root level. Owning the box, means take the system & prevent the admin from controlling the system, as well as preventing other hackers from getting in. So hackers usually move on from the regular level, to the admin level so they can have full control. A hacker needs privilege escalation to compromise the system well. Some exploits allow buffer/stack overflows to obtain admin access. All it takes is a guest user, then a hacker can perform exploitations locally and there he goes to the root.
At this point, we did everything up to owning the box. Now our goal is to protect our access. Thus, we want to maintain our access to that hacked system, so we can use it later. You can maintain a system by using such tools, backdoor accounts, backdoor software programs, rootkits, etc. These tools help you maintain access. Some hackers own the box close all other accounts except his account, so the security person shut the system down, reformat the system and start over again.
By doing this, hacker account will be gone. Once we ensure we have maintained our access to the system, then we want to expand ourselves to other parts of the network. Remember, if you do not do this on your own network, somebody else will take care of it. If he does, i do not think you will be too happy! Once you got an access, and could maintain it successfully. You want to prevent detection or loss of access. There are several methods to maintain access, such as rootkits, OS exploits, erase tracks, install trojans that make you access backdoor, enable null sessions (webmaster usually go to the registry & disable null sessions to keep that vulnerability from being exploited, webmasters usually do it once and do not get back to it. You can go there & enable it - NOTE: by enabling null sessions you can give other hackers a chance to hack too), and many more.
There different ways of system compromise, system compromise usually depends on your goal, examples of system compromising are root access(ultimate goal), data access/theft, DoS, and many more. Keep in mind, compromised systems can be detected after a while.
Now after a hacker breaks into the system, he tries to protect what he has hacked & erase his tracks. During the attack process try not to be detected so the webmaster don't shut the server off, as well as do not forget to erase your tracks, e.g. you don't want the webmaster to see lots of failed logon in the log files, so you erase tracks to prevent future detection. Typically, get in the network as a shadow or ghost.
There are many method to evade those IDS so they don't cut off your attack stream. Common methods for evading defenses might be by fragmenting packets(some programs do that e.g. fragroute), port redirects, encoders(change the flow, the look, and feel of various traffics to pass firewall). After you get in and deceive defenses, you want to go to the log files and erase your tracks. Remember: sometimes you get in a user account then you get into a root by changing permissions of the user account, so you have to remember to set this user permissions back to as it was, things like that - you know what i mean, put yourself in a hackers shoe. Don't delete the whole log files, this can make the security person more suspicious. We want to leave everything as it was so nobody can get a feel that an intruder was here.
To be safe, you should know where your actions are recorded, delete log files and other evidences that can get you caught, steganography (Google it), and evading IDS & firewalls. All actions are recorded in some place on the system or the network. Assume IDS detects you, what do security persons do? Usually when you get detected, they may cut off all the ways for you so you don't get a chance to penetrate, they probably going track you down, or they may decide let you go but watch you the entire time.
Where are your actions recorded and what things can let security person knows that you hacked his system? they are recorded in log files for various applications(e.g. IIS & Apache log files), file access times(note: there are tools for hackers that allow you to modify file access time), windows registry entries, hacker tools left behind (be aware of the residual configuration you have left behind - make sure you set all the configurations back to as it was), OS performance stats, IDS, proxy servers(make sure how you send and receive data. If you are going to use proxy server, set up a permanent tunnel through the proxy to the remote host that is compromised), and firewalls(usually very rich with logs).
There are various types of IDS, IDS can set anywhere in the network. There are network based IDS, host based IDS, and application based IDS.
Deleting evidences of your hack is extremely difficult, it requires you have a very high knowledge of the system you are trying to compromise(all the prior steps we did, such as scanning, foot printing, etc will be handy to compromise the system). It is easy to cover the known log files, such as web logs, firewall, IDS logs, etc. However, it is important to know how the default logs work. Highly skilled hackers, study the target well & take the time in fingerprinting & footprinting everything properly. It may take him up to one week before he hacks the target, but when he penetrates his job is done more smoothly & quietly. Unlike, the other ones who are just using some tools to break the system as fast as possible without studying the target well.
It is possible to delete log files! It is simple but usually requires admin access. Some files/logs may be deleted automatically with reboot. Don't delete log files, it brings up suspicion. If you do so, the security person can indicates very clearly that a hacker broke into the system.
Most common way of hiding your tracks is by using a rootkit. Rootkit is set of tools used by an attacker after the attacker gets the root-access to system. Rootkits conceals(to keep from being observed) attacker activities on the hacked system. Once rootkit set on the system, its practically impossible to rid of it because rootkit uses technology, called "hooks", that usually most of the time embed itself into various components of OS & effectively the OS going to be a toaster when the rootkit is all set and done. Security person has to rebuild his machine when rootkit is detected after we properly investigate it.
Steganography its about hiding a file into another file. Like hiding a malware into a normal software which makes it difficult for firewall or AV to detect the malware. That's the basic concept of Steganography. There are alot of tools out there allow us to hide files inside another files.
You can evade IDS & firewalls by using random slow stealth scanning technique so traffic goes unnoticed, this takes longer to scan but makes detection more difficult. Try to use non-standard techniques, think outside the box.
Remember: not everyone out there is a security expert. To secure your system well, you need to put yourself in a hacker set of mind.
By now, you have learned the basic methodology that hackers use to break into the system. Anyhow, lets take a closer look on hacking techniques, such as encryption, sql injection, sniffers, and many more.
Encryption: files can be encrypted in a storage. Communication channels can be encrypted as well, communication channel encryption encrypts the entire communication path, so all traffics sent and received are encrypted, e.g. SSL technology encrypts the entire communication path. There are many ways hackers get away of encrypted traffic & get info in not encrypted form. If you are using your own encryption method, you always should test your encryption for crackability before you use it officially.
Sniffers: sniffers is a common tool used by hackers. Sniffers listens on any traffic that goes through the wire of the target system, listens ins and outs traffics. Promiscuous mode is a mode that is listening for any traffic that goes through the wire. Standard promiscuous mode sniffer is a basic technique. There are more advanced techniques other than promiscuous mode. Sniffing enables the attacker to pick up a plain text, and other sensitive data that goes 'from' or 'to' the target. Sniffers record captured traffic, then after you sniff you can go offline & start analyzing that captured traffic. Popular sniffers are ethereal, etherape, ettercap, and network monitor(for Win OS only - not so effective).
Wireless Hacking: this is a new technology & starts taking place nowadays. Easy to setup, but not frequently secured since not many people understand the security configuration, so they decide not to set it up or set it up poorly. There are various tools that detect wireless networks, popular war driving software are Netstumbler, Airsnort, Airopeek, Kismet, and many more. What is war driving? Google it!
SQL Injection: sql injection is a technique that allows an attacker to steal a valuable database information. This attack relies on poor data validation and poor error checking.
Buffer Overflows: buffer overflow is common, the cause of buffer overflow is poor coding. Buffer overflows might be noticed while coding. Buffer overflow happens when the programmer does not clearly define boundaries on buffers or variables. We use out of bound data to insert malicious code or execute command on the remote host. Buffer Overflows can cause programs to freeze or lockup, can cause machine to crash, or let you use exploits & leads you to compromise the system. To build buffer overflows, you need a good programming skills, good knowledge of stack and buffer vulnerabilities.
You need to have the ability to research, analyze vulnerabilities & apply the exploit to achieve what you want. Buffer overflow is a very common & hard to produce an application with no buffer overflows at all. There is nothing programmers can do about it, they just need to write the code with security mind of set. If unexpected buffer overflow appears later by chance, programmers will have to fix it. Programmers should test their code from vulnerabilities as much as they can before they publish the application.
Rootkits: it is a common hacker technique. Rootkit is malicious program that replaces components of OS. It does a stealth job. Rootkit requires root permission, so you can install it. Linux rootkits are common & you can find them everywhere, unlike Windows. It is very hard to detect a rootkit because it embeds itself so deeply into the target system. Removing rootkit from a system is very hard too, if the security person tries to remove the rootkit out of the system, he will destroy the system since the rootkit is embedded so deeply into the system(into components of OS). The good solution is to format the whole system & install it again.
Spoofing: the word spoofing defined as making yourself appear as somebody else. Examples of spoofing, you can spoof an IP address and make yourself appear to be somewhere else, MAC addresses, and emails(very simple to spoof, you send an email to somebody by changing the headers, and things like that). Spoof usually relies on poor implementation of TCP/IP itself or poor implementation of applications. Tools that are used for spoofing differs from one platform to another. Example of the tools, IP spoofing utilities, MAC address modifiers, etc. Spoofing is more into using your skills rather than using a tool.
Denial of Service (DoS): DoS is very common. The ultimate idea is to prevent legitimate users from using the system. Running DoS is very simple, you don't gain anything from doing DoS. Hackers do it to threat companies, things like that. Many methods/level of DoS attacks exist. Examples of some ways of to DoS, ping of death, Windows size overflow, smurf, teardrop attacks, and many more. There are lots of different ways to do it!
Web Hacking: web hacking is the most popular attacks. It is based on hacking individual sites, servers, or components based on the website. First step a hacker takes is, enumerate services(applications) on target machine, and then determine what webserver software(apache, IIS, etc) is running on the target system. After that, the hacker exploits against vulns. found in the target system. It will be easier to hack if the hacker knows the version of the service/software running.
A webserver attack leads to deeper penetration on the network(move into the target's internal network). Popular attack methods are xxs(cross-site scripting), IIS DLL vulnerabilities(IIS is very commonly exploited), directory traversal, unicode attack, and many more.
What is Unicode attack?
here is quick rough description about Unicode attack, lets say you want to pass space into a URL. If you put a space in URL, webserver will not take your URL, webserver will consider the url is invalid. Thus, if you want to put spaces among the URL, you should put the number 20 in a place of the space(number 20 represents the space), so when the URL goes to the webserver, the webserver says Ok! thats a valid URL, lets process it and so it does. Unicode attack uses this technique in a non-standard(bad way) way to attack the webserver. Thats a quick explaination about unicode attack.
I'm already about to finish this tutorial, i will just talk about popular tools in a brief manner. I will start with nmap.
Nmap is the most popular hacker tool out there. Linux command line nmap works better and is supported better. Nmap comes with ping utility, port scanning utility, service enumeration & OS fingerprinting.
SuperScan is a windows based tool developed by foundstone Inc. Its easy to use it & a good tool for Windows.
Nessus is used for vulnerability assessment. It is an open source software kit, with commercial version available as well. Nessus uses client/server architecture. Server will be installed on a central location. Nessus comes in GUI & command line interface. Nessus uses database that carries latest current exploits for all types of OS & application. Databases in nessus are called plug-ins, hundreds of vulnerability plug-ins exist and are updated daily to include latest exploits. Nessus requires high level of knowledge to use the tool very efficiently. You can go out to the web and download an exploit and then add it to the database. Nessus can take quite long time to do vulnerability assessment.
Finally, the information in this tutorial have been gathered from various types of sources, and then i wrote the tutorial in an organized manner from scratch as well as i added some stuff & clarified many parts.
After you have read this tutorial, i recommend you to search and learn about Windows Null Sessions, it is the most critical flaws associated with Windows OS, and google about DNS zone transfers!
This tutorial is a good guide for you that gives you an insight on how to start & different techniques that hackers use and how they are used. I hope you have enjoyed this tutorial & helped you in someway or another. I'm not supporting any illegal activities. This tutorial for people who wants to know how hackers think, what steps they take to break into systems & how they do it, so people can have an insight on how to protect themselves against intruders.